|
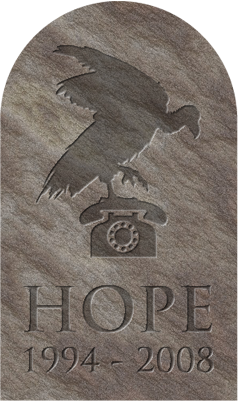
2008 "THE LAST HOPE"
(Excerpts
of related media coverage.)
"... Avatars beware: Private
investigators scouring Second Life (REUTERS)
Tue
Jul 22, 2008 2:13pm PDT
Be
careful, that avatar on your sim could be a real-life private
investigator, sent in to report on what you’re up to in your Second
Life.
Last weekend, veteran private investigator Steven Rambam
of detective firm Pallorium
came to New York to give a talk about
privacy and investigation techniques at the Hackers On Planet Earth
conference. After Rambam told attendees how he tracked down one target
inside Second Life, Reuters caught up with the private detective to
find out what happened.
Rambam’s client told him this story:
Twenty years ago as a child, he had been molested by one of his grade
school teachers, a trauma he never fully recovered from. “The client
believes/d that pedophiles don’t ‘retire’ — I absolutely agree — and he
wanted to prevent the target from molesting anyone else,” Rambam said
in an email. “We were retained to investigate, gather evidence, and if
evidence was found then convince the target to retire from teaching.”
So
Rambam started looking into his target — now an assistant principal —
and discovered the man was a Second Life user. Pallorium
investigators
logged into Second Life and tracked down the man’s avatar, only to
discover his Second Life identity was a leather-clad dominatrix
(pictured below).
Not that there’s anything wrong with that.
“The avatar by itself would not have been conclusive evidence of
anything,” Rambam said. “The most significant evidence that we gathered
was collected old-school: we identified other possible victims,
interviewed them, and one person told a story very similar to what we’d
heard from our client.”
But Second Life users should be aware, Rambam noted, that investigators
are increasingly well-versed at using the virtual world.
Rambam
caught a lucky break in tracking down the man. When Kevin Alderman
hired private investigators to track the real-life identity of avatar
Volkov Catteneo, Alderman had to work from IP addresses. Without giving
away the tricks of his trade, Rambam said he came across his target’s
avatar name “during a very preliminary phase of our investigation.”
...".
"...July
20, 2008
The
Internet -- a private eye's best friend (CNET)
(CNET:
Elinor Mills)
NEW
YORK -- For private investigator Steven
Rambam, the Internet is his
most valuable tool in helping to find missing persons and your
competitor's dirty secrets
(PHOTO: Steven Rambam, director of
investigative agency Pallorium, tells the crowd at the
Last HOPE conference that "privacy is dead.")
But
while the intelligence business is booming, individuals are losing the
battle to protect their privacy with every blog post, Google Web search
and online photo, Rambam, director of the Pallorium investigative
agency, said in a keynote session late on Saturday at the Last HOPE
(Hackers on Planet Earth) conference.
"Anything
you put on the Internet will be grabbed, indexed, cataloged and out of
your control before you know it," he told CNET News after the session.
"The genie is out of the bottle. Data doesn't stay in one location. It
migrates to hundreds of places."
Information
that he used to have to search for or dig up in far away places is now
available at his fingertips. All types of information is being
digitized, older stuff is being scanned and put online and it's all
being aggregated into uber-databases that are being sold to marketers,
government agencies and anyone else who can pay, he said.
Rambam
says he searches on social networks to find photos of what people he is
researching look like, the first step in any investigation. He gets a
lot of other vital data from those sites, like hometown, age,
relationship status, school and work history, hobbies, and friends and
acquaintances to interview. With Twitter, he can often see where they
are right now, or at least in the recent archived past. ... " .
Radar
O'Reilly (Tech Blog)
"...I
made the trek to a steamy hot NYC this weekend to attend one day of the
three day Last HOPE (Hackers on Planet Earth) conference at the Hotel
Pennsylvania. There was too much going to adequately cover it here (or
even take it all in), but a few things stood out.
Steve
Rambam's eye opening talk on the death of privacy for
example. For a
solid three hours in front of a standing room only crowd he weaved back
and forth between the Orwellian theme of how our privacy is being
ripped from us by everyone from Google to Choicepoint and the theme
that seemed even creepier to him, self contribution. Over and over he
expressed disbelief at how willingly we post our personal details
everywhere from Twitter to Facebook while thanking us all the while for
making his job as a private investigator that much easier. What the
marketers and government don't actively take, we actively give.
Naturally I twittered the whole thing.
Cell
phone tracking; artificial-intelligence-assisted reality mining; 3000
cameras per square mile in Manhattan; facial, activity, and even gait
identification software; government outsourced investigative databases
shielded from FOIA requests; UAV-based license plate scanners; beating
anonymity by correlating multiple datasets; unanticipated database
repurposing; and on and on... Finally I could twitter no more and left
the venue hurriedly fashioning a tinfoil hat from a burger wrapper
while consigning myself to doubling the dosage on my meds.
I
will say this though, there was something deliciously ironic about
standing in a room chock full of hackers all listening at rapt
attention to a three hour chillingly dystopic harangue on privacy loss
while nearly every single one of them was wearing an RFID tag around
their necks. Even better, the tag was tracking their every move around
the venue and was linked to a comprehensive self-contributed profile.
...".
...
"...I expect video for some of the talks will pop up here and there. In
the meantime, if you are interested, these guys videotaped every
session and made DVD's. If you don't already suffer from paranoiac
delusions I would highly recommend Steve Rambam's session ...".
|